Commits in git can be signed cryptographically using a GPG key. In git, it is trivial to add anyone as a commit author and a bad actor could use this feature to introduce malicious code into a project and hide the real identity. A commit author can be added at commit time by adding an author flag like this:
--author="John Doe <jdoe@example.com>"
Signing commits using GPG keys helps ensure the commit’s author is actually who they claim to be. In this article, I will show you how to create GPG keys and sign commits using them.
Required software
You’ll need to have the following tools installed
- Git
- GnuPG. If you’re on Windows, install GPG4Win from this website. Most Linux distros typically come with GnuPG pre-installed, so you might not need to install it if you’re a Linux user.
Generate a new key
After downloading and installing the GPG tools for your OS, run the following command in the terminal to generate a new GPG key pair:
gpg --full-generate-keyNext, at the prompt, specify the kind of key you want or press the Enter key to accept the default.
At the next prompt, specify the key size you want. GitHub recommends that your key size be at least 4096 bits.
Enter the length of time the key should be valid. The default selection is for a key that doesn’t expire.
Verify your choices, enter your user information, and secure the private key with a secure passphrase. You will need the passphrase later to unlock the private key when making commits.
Once you complete the steps above, verify that your key was created by running:gpg --list-secret-keys --keyid-format=long
You should see a list of keys, including the one you just created.
The next step is to generate and copy your public key to your Git server(GitHub/GitLab/Azure etc). Substitute <key_id> with the ID you copied in the step above:gpg --armor --export <key_id>
This will print the GPG key in ASCII format in the terminal. Copy the GPG key, including the ----BEGIN PGP PUBLIC KEY BLOCK --– and the ----END PGP PUBLIC KEY BLOCK ---- and add this to your Git server.
Exporting and importing existing keys on different computers
Skip this section if you don’t need to export an existing key. In most cases, the secret key does not need to be exported and shouldn’t be distributed, but if you need to back it up or use the same key-pair on a different machine, run the following command:
gpg --export-secret-key --armor <key_id> --output private.key
The --armor flag creates an ASCII(non-binary) representation of the key.
To import the key on another machine, do:gpg --import private.key
Enabling commit signing
Tell git to sign your commits by running the following commands:
git config --global commit.gpgsign true
git config --global user.signingkey <key_id>
Next, tell git which GPG program you want to use. If you’re on Windows, this will probably be:git config --global gpg.program "C:\Program Files (x86)\GnuPG\bin\gpg.exe“
Conclusion
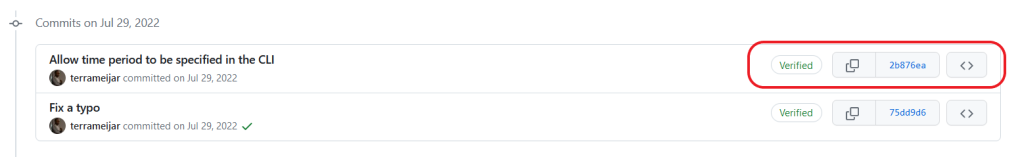
If you have everything configured correctly, you’ll get a prompt whenever you make a git commit, asking you to provide a passphrase to unlock the private key and your commits will have a “verified” badge in GitHub: